LinkedIn is a social network used for professional purposes: finding candidates, finding a job, and representing a company or one's own professional qualities. So, LinkedIn can be useful for investigators, as the work takes up most of the day for most people.
With Linkedin, you can track professional and personal connections, a person's career achievements, or a company's reputation. Moreover, this social network can give a good impetus to further research of open sources.
That's why we want to tell you how to use LinkedIn correctly in OSINT investigations and what information you should pay attention to.
People search
LinkedIn has a complex system of permissions that closes profile information if you are not in a person's contacts. This system can make things more difficult if you find the target's contact page, but you can't see their page without being added to the contacts. It is better to use a Google search or modification of URL links in this case.
Enter google dork site:linkedin.com "title" in the search, replacing the word "title" with a short description, which is usually written under the person's name, such as "CEO of Facebook". By clicking on the search result, you can see the information on the page without authorization.
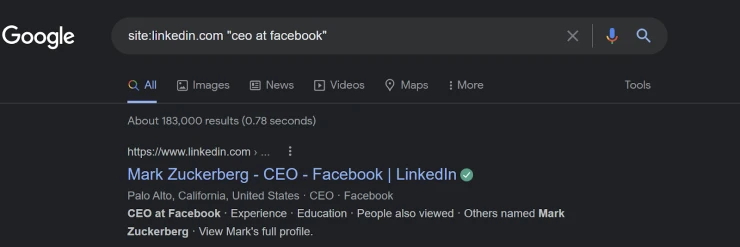
The same trick works if you use a link:
https://www.linkedin.com/search/results/people/?company=facebook&title=ceo
So you can find all the people who have such a position. By the way, this is also a helpful feature if you only know the role of a person or part of their name. In this case, you need to enter the known values in the URL.
Find a person's email
One of the most valuable things for an OSINT investigation is a person's email address, as social networks, phone numbers, and even bank accounts can be connected to it. So, it is worth starting with an email search using LinkedIn.
Finding an email is usually quite simple if you have a person in your contacts. Click on a person's contact and the "show more" icon to make a window with the email address appear on the screen.
If that doesn't work, try using online tools like Swordfish. This resource can find an email and phone number if you enter the Linkedin URL in its search engine. Still, you need to register to get five free searches.
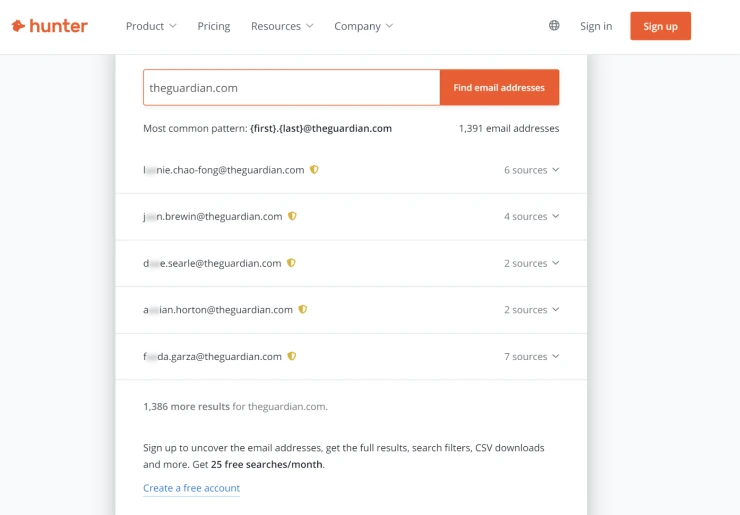
Another way to find out the email address of a person is to use their work data. First, if you know the emails of your target's colleagues, you can try to guess the email using the same algorithm. For example, if Denis Black's email address is [email protected], her colleague Sirius White would have an email address of [email protected].
However, a surer way is to use Hunter.io, which finds all email addresses with a corporate domain, such as bbc.com, theguardian.com, etc. In addition, this service shows if the email was mentioned in open sources. So, if you find a person's page on LinkedIn, you know where they work, and you can see their email domain. Unfortunately, the search only works if the company has not blocked its display on such services.
Investigate pictures
Studying the profile picture and background photo is also beneficial as it can give us additional information. For example, you can use reverse image search using Google Images, Flickr Image Search, or TinEye. Once you find other versions of the photo, you can scan it for Exif data and find out where and when it was taken if you are lucky.
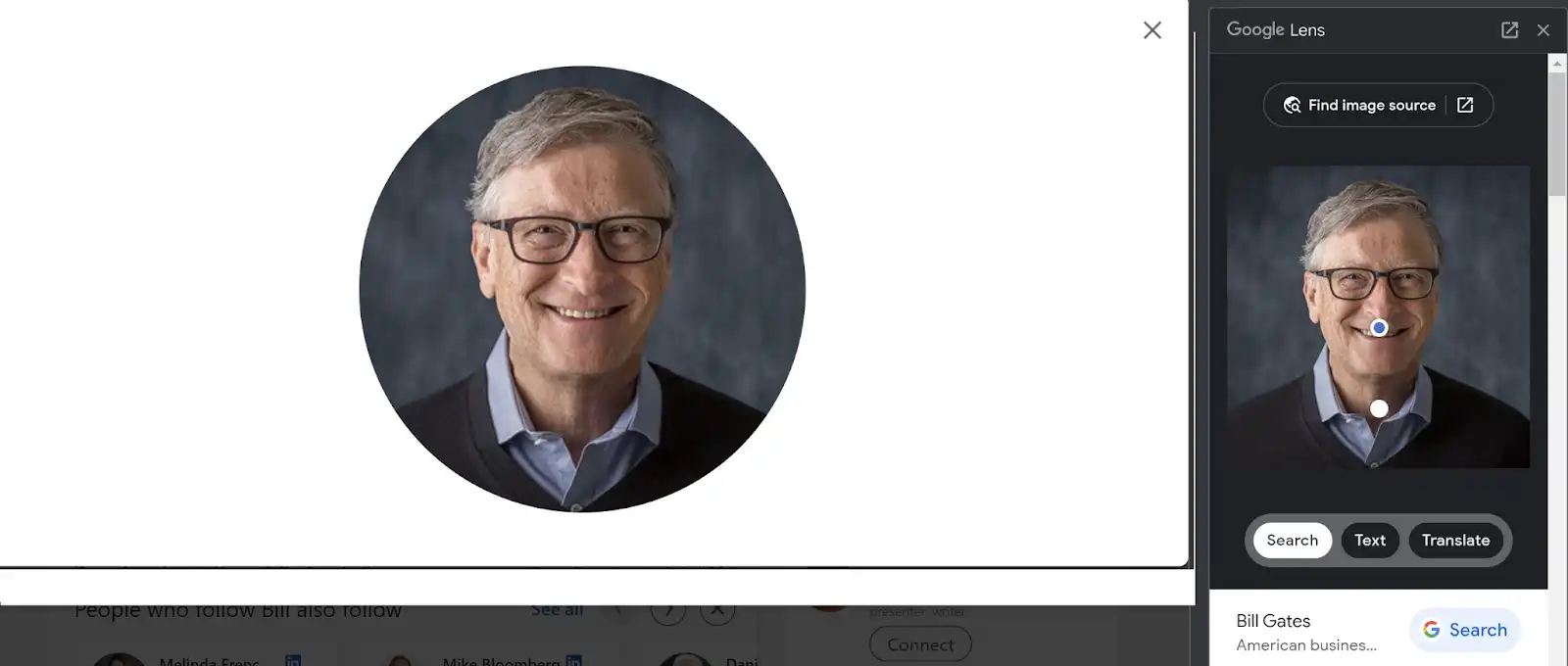
Or, just use your deduction. You can enlarge the picture by adding the “/detail/photo/” parameter into the URL string to see what is left behind the frame. It might show you some important details about the location or other prominent clues. You can also do it with a background photo to gather as much information as possible.
Check username to find other social networks
The username is always reflected in the URL and most often matches the real name of a person since LinkedIn generates it automatically. Still, sometimes they can be different if a user has changed the auto-generated version. In any case, try to find profiles on other social networks using your target’s username.
You can do this through the search engines built into each social media, for example, Instagram. Or I use Google Dorks or or URL to cover all possible versions.
For example, if you are looking for John Lukas, you can enter multiple username options at once:
site:fb.com “johnlukas” OR “johnlukas” OR “john_lukas”
Or use URL, although it might be less accurate:
https://www.facebook.com/johnlukas
This method also works with other social networks, so you check all possible options.
Search Linkedin profile's recent activity
Linkedin is a social network for professional interactions, and people share information as part of that interaction. For an OSINT investor, such activities can also be helpful if people talk about the latest achievements and failures of the company, their interaction with other people, and their opinions on various issues.
The best thing is that you can view activities on a user's page, even if you don't have them in your contact list, using the URL modification:
- Adding /detail/recent-activity/ after the username allows you to view all recent posts, documents, or articles.
- Pressing “All activity” shows you all activities, including likes and reactions to other users' posts.
Conclusion
Although LinkedIn is a pretty closed network for outsiders, a couple of tricks will help you build a complete portfolio of your target, including photos, interaction history, and contacts. If this information is not enough, LinkedIn can be a push for a broader search, especially if you manage to access the person's email address.
So don't neglect this social network, even if you can't gather much data at first glance. If you use the right tools, anything is possible.
***
📌 For everyone who really wants to learn OSINT, we recommend OSINT training courses from Molfar:
▪️ Basic: for personal study and receiving a knowledge base + all the necessary tools for work.
▪️ Advanced: for scaling processes, gathering a team and learning HUMINT.




